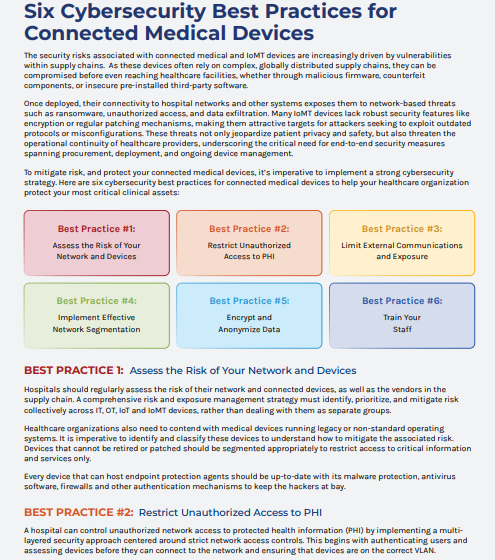
Six Critical Cybersecurity Practices for Protecting Connected Medical Devices Once deployed, their connectivity to hospital networks and other systems exposes them to Read More
Guide to Achieving DSPT Compliance We live in an era of increased cybersecurity activity. Beyond uptime and availability, privacy and security are Read More
How to Create a Mobile Device Security Policy, With Template A mobile security policy is vital to securing an organization’s work Read More
4 Types of Mobile Security Models and How They Work An IT admin often has to find the best tools and practices to Read More
Leading financial institution ensures their Avaya contact center is production ready just two-weeks before go-live Two weeks before a leading Spanish financial Read More
Using AI to enhance food and beverage innovation After all, AI has long since become part of everyday industrial life and is Read More
Optimized & Sustainable Operations In Food and Beverage The following technology integrations collectively contribute to the development of optimized and sustainable operations in Read More
How to Sell with Al You can’t sell with AI without an AI sales tool. AI doesn’t exist without boundaries Read More
How to Book Meetings Like the Top 1% with Apollo Booking meetings like the top 1% with Apollo isn’t about sending more messages—Read More
5 IT Operations Management Best Practices You Need to Know ITOM teams are an incredibly important part of an organization. The team’s Read More