PowerVault ME5 for Virtualization Modern IT environments increasingly depend on virtualization to consolidate workloads, improve agility, and reduce operating costs. To fully Read More
Freedom and Compliance with Self-Service Environment Management Initial provisioning is just the start. The real challenge is Day 2 Operations – the ongoing lifecycle Read More
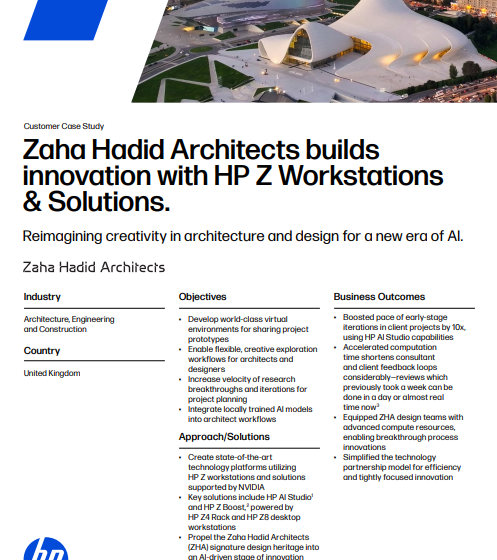
Zaha Hadid Architects Builds Innovation with HP Z Workstations & Solutions The first woman to be awarded the prestigious Pritzker Architecture Prize in 2004, Read More
Unlock Productivity for Your Team’s Most Complex Workflow Spec’ing devices based on single software workflows no longer reflects the reality Read More
Defense in Depth: A Layered Approach to Mobile App Security In recent years, the mobile app industry has seen an increase in Read More
A Comprehensive Guide to Mobile App Security Most of the time we spend with our smartphones today centers on mobile apps. In Read More
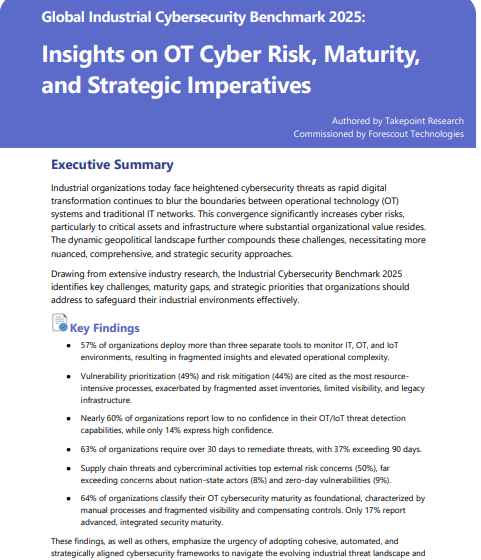
Global Industrial Cybersecurity Benchmark 2025 Industrial organizations today face heightened cybersecurity threats as rapid digital transformation continues to blur the boundaries between operational Read More
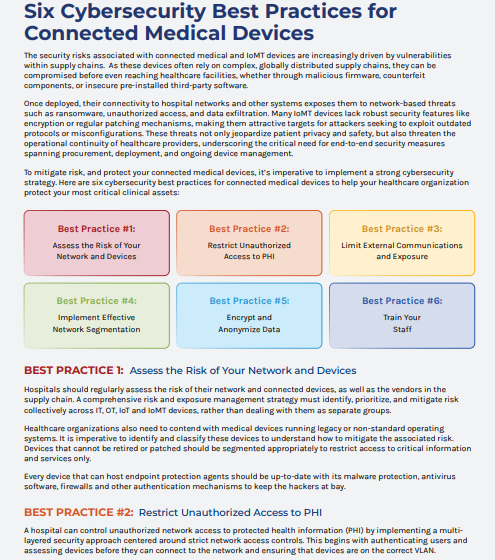
Six Critical Cybersecurity Practices for Protecting Connected Medical Devices Once deployed, their connectivity to hospital networks and other systems exposes them to Read More
Guide to Achieving DSPT Compliance We live in an era of increased cybersecurity activity. Beyond uptime and availability, privacy and security are Read More
How to Create a Mobile Device Security Policy, With Template A mobile security policy is vital to securing an organization’s work Read More